The 5 Steps I Took to Recover My Hacked Blog

My blog, Leaving Work Behind, was hacked in April. It’s something you read about often enough but never really expect to happen to you until it’s too late. To be honest I didn’t see myself as a prime candidate — I’ve written about WordPress security often enough to have plenty of preventative measures in place. However, those measures were clearly not comprehensive enough.
Getting hacked is something I do not want to go through again. There are so many reasons why website downtime is bad for your blog/business: while a loss of traffic and potential income are the two most obvious, I cannot understate the amount of time I lost in getting the site restored and the amount of stress it caused me.
In this post I want to reveal what happened to my site and let you know what I have done to increase the security of my site since.
Getting Hacked: My Story
I woke up on Thursday 18th April to find that my site was down and had been for a few hours. I immediately contacted my hosting provider, Westhost, who informed me that their ModSecurity firewall had detected unusual activity on my site and had shut it down immediately as a precaution. Upon running an initial restore on the site I could immediately see that it had been hacked. While the changes were relatively subtle, it was clear enough that some unscrupulous sort(s) had been nosing around.
It turns out that a huge number of WordPress sites had been hacked too, and Westhost had their work cut out. Fortunately they take daily backups of the site and by the following afternoon I was back online with a version of my site that was as close to current as possible.
Here’s the effect the hack had on my traffic:
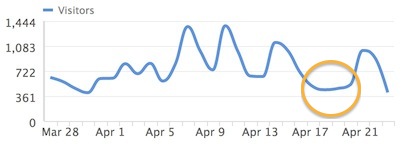
To put the above graph into perspective, that week’s traffic was down ~30% when compared to the previous week. That theoretically meant a 30% drop in income.
It is fair to say that I was keen to ensure (to the best of my abilities) that such a hack could not be repeated. I took action immediately.
My Immediate Steps
The first thing I did was to verify that I had been following the steps outlined in my recent post on securing your WordPress website.
These were the absolute fundamentals: updating my themes and plugins, ensuring that I had a recent backup, ensuring that my default profile was not named “admin,” changing my password, and checking for security plugins on my site. With those items in place it was time to move on.
I am under no illusions that my site is now 100% secure — after all, there is no such thing as a 100% secure site. Having said that, I know it is far more secure than it was before and I will continue to research site security measures now and in the future. So far, this is what I have done.
1. I Installed VaultPress
For those of you who don’t know, VaultPress is a totally automated backup and security solution for WordPress. It it owned by Automattic, the de facto “owners” of WordPress.
Having been using VaultPress for a few days now, I can’t believe I was so cheap to have not stumped up for the service beforehand. Their base package starts at $15 per month — I’ll pay that for peace of mind any day of the week.
In fact, I chose to go with their Premium package ($40 per month) which includes:
- Realtime Backup
- Automated One Click Site Restore
- Archives, Stats and Activity Log
- Priority Disaster Recovery
- Priority “Concierge” Support
- Daily Security Scanning
- Security Notifications
- One-Click Fixers for Security Threats
- Site Migration Assistance
Basically, they’ve got you covered.
While VaultPress cannot guarantee your site’s security against hackers, it pretty much can guarantee that your site can be restored with relative ease. There’s just something very calming about seeing hourly snapshots of your sites stored on VaultPress’ servers:
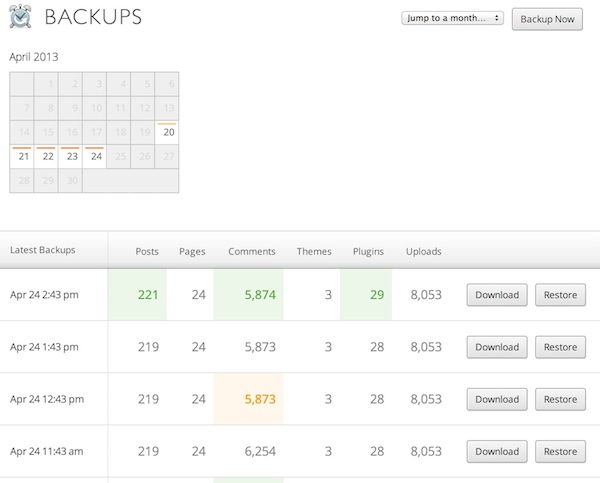
While there are plenty of free backup solutions out there, I don’t think anything beats the relative peace of mind I get from VaultPress. They’ve got 90 snapshots of my site available to restore right now, of which the most recent is just twenty minutes old. I know my site is safe in their hands.
2. I Managed My Profiles
A hacker can potentially access your site from any of the administrator profiles within your WordPress backend — not just the one you use. When I loaded up my profiles I could see that I had three other profiles — a guest poster profile, and two other profiles for (trustworthy) people I had given access to my site.
I began by shutting down those two profiles and changing the role of the guest poster profile to Author. This is something I would advise you do — only create as many Administrator profiles as is absolutely necessary. Additionally, you should of course ensure that each account as a suitably random and unique password and that said passwords are regularly changed.
There are times when you will need to allow people (such as your web designer) access to your site. In such situations I advise that you create a profile for them with a new password, then delete that profile as soon as its necessity comes to an end.
Always be thinking about your site’s points of entry and whether they are strictly necessary.
3. I Changed My Passwords
You may think this was an obvious move, but I’m not actually talking about my WordPress passwords. Although I did change them, I was also sure to change all passwords to particularly sensitive accounts, i.e.:
- Gmail
- My Hosting Account
- Amazon Associates
- Etc
If you’re wondering why I made this move, just consider the story of Mat Honan, whose entire digital life was destroyed by hackers who originally hacked into his Amazon account. If you feel in any way blasé about online security then the above article is a must-read.
Consider this simple chain: a hacker gains access to your email account from which you recently sent an email to your web designer with login details for your WordPress site. That’s all they need to gain access to your site and do as they please. Hacking can be that elementary.
4. I Upgraded to SFTP
Here’s something you may not know: any data that you transfer via FTP (including your username and password) is completely unencrypted. Therefore, anyone who is successfully able to intercept FTP transfers will be able to pickup your login details and gain access to your account.
Not only does this allow them to add and remove files as they see fit, but they can also gain access to your WordPress database via phpMyAdmin and ultimately login to your site.
Put simply, it doesn’t matter how secure direct access to your WordPress site is if they hackers can get in via FTP. As such, I strongly recommend that you disable FTP access to your site and transfer files using the alternative SFTP protocol, which does encrypt data. Any good hosting provider should be able to help you with this.
Speaking of hosting providers…
5. Consider the Suitability of Your Hosting Solution
I am glad that I’m with Westhost. It was their ModSecurity firewall that spotted the hack in the first place and shut down my site before serious damage could be done. They also carry out automatic daily backups (which were used to restore the site) and have cracking customer support to boot.
Can you say the same for your hosting provider? There are so many great options out there that you would be crazy to stay with a provider you are unhappy with. You might consider switching to one of the managed hosting solutions (like WPEngine) as WPExplorer did just recently.
Whatever your choice, be sure to inquire as to the security measures they take. Consider the measures I have taken above and ensure that they are compatible with your hosting solution.
The moral of the story is this: do not compromise on security. Ultimately, keeping your site secure is more important than anything else. There’s no point having great content or a spangly new design if no one can see it because your site has been torn to shreds by ruthless hackers.
Nefarious types who have nothing better to do with their lives than hack people’s sites are not going to go away any time soon. The sooner you accept that and take reasonable measures to protect your site from being attacked, the better for the long term security of your online assets.
I would love to know what you think about the measures I have taken. Are there any additional recommendations you would make? Let us know in the comments section!



unfortunately happened that an online friend’s blog to be hack at this time can not access to the blog 😐 lost 2 years work online,very interesting your article…
Useful post Tom, sorry to hear about your hack! Some useful resources here, VaultPress has been on my radar for a while as too has WPEngine. Seems if anyone is serious about their security its a small price to pay.
My thinking exactly Elliott — VaultPress just works, and works beautifully. Well worth the money.
i dont know if i have been hacked, all http request on my wordpress site cant find host, on my dashboard i have all kind of http error also i cant search or instal plugins automatically it will not search, will say there is problem with my server configuration, also google ads not showing on my site as google said they cant access my site due to connectivity error.
Try checking your site with the free tool here: http://sucuri.net/
It is high time to secure WP blogs. Thanks for the tips. Will try these.
No problem 🙂
Is there any plugin can give an instant warning to you when someone trying to access your WordPress webiste?
Good question. I’m not sure about an instant warning, but I did a quick search on WordPress.org and found these two helpful little plugins:
1. Login Alert
2. WP Security Login Notification
good post. I wanted to share one of my experience here. My website got hacked last week, and it was such a mess. I had 10 other websites hosted on my same FTP server, and they were all being redirected to some weird website I worked on it for probably 4 days. am not able to fix it. Then i started looking for professional help. I found a website called totalwebsecurity.com/ and worked with their technicians. They had my sites completely fixed, up and running in a day. The whole thing costs very less, I’d recommend them to anyone.
Thanks for sharing Steve, I’ll check them out!
Great article! Thank you for sharing your own experience about recovering site from Hacking.