How NOT to Secure Your WordPress Website

What is the first thing you would do when you want to secure your WordPress site? Find out the top five security plugins, consider how affordable they are and then go ahead and install one. That done, now you can sit back and relax, right? Wrong!
Using a security plugin does not ensure security. Security is not an absolute thing and no one can guarantee complete security. The best we can do is reduce the risk of a hack. And contrary to popular belief, the site owner needs to be involved in keeping the website safe. Knowing what you should do and shouldn’t is significant.
While there are several guides to what you should do to keep your WordPress site safe, we are offering you a guide on what you should AVOID doing instead. You will note that the advice here are in conflict with the general belief. But from our experience, a lot of advice out there are outdated and offers a false sense of security.
If the matter of WordPress security nags you as much as it does to us, take a look at the following.
1. Don’t Use Too Many Security Plugins
Given the wide range of plugins available out there, with various feature sets, it’s tempting to use more than one WordPress security plugin. To be honest, it’s an overkill. Being anxious about your site’s security is normal but you have to ask yourself if you really need more than one security plugin? What are the features essential to your site’s requirement? Are the features going to step on each other’s toes?
For instance, a conflict could arise when the plugins begin modifying files such as wp-config.php or htaccess. Plugins can easily fiddle with these files but they are not modifying them in a single unanimous way. This could create conflicts and make your website slow.
With WordPress sites, things can go wrong now and then. Everyone hates the dreaded White Screen of Death. Having multiple plugins that deeply affects your website can make debugging issues difficult. Now, had there been just one plugin, finding and fixing the cause of the error would have been easier and less complicated.
2. Do Not Change DB Prefix
There are several ways in which a WordPress site can be compromised. Hacker may gain access to a site’s database through SQL injection attack. A vulnerability in a plugin or theme can be used to break into the site’s database (which is why we suggest you instead use a WordPress database backup plugin to avoid similar pitfall). One popular method of preventing hackers from going deeper into your site is by changing the default table prefix. As you can see in the image below, in WordPress, the default table prefix is ‘wp_.’ WordPress allows you to change table prefix (to say, ‘xzy_’) so as to hide certain tables.
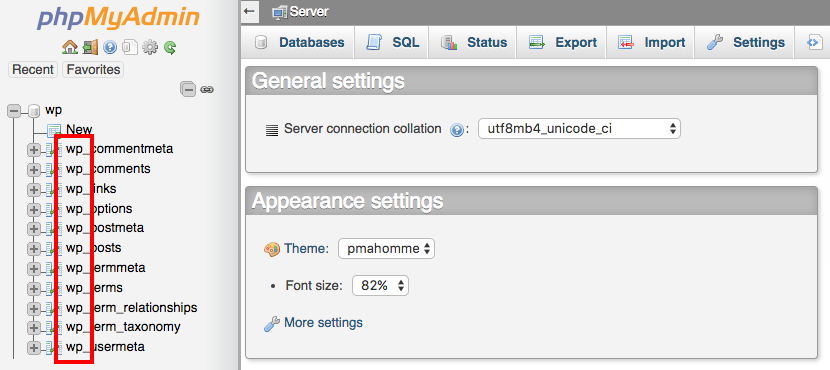
On the surface, this looks like a good idea. If the hackers do not know the table name, then they can’t retrieve the data from it. This is, however, a false reasoning. Once someone hacks into your database, there are still ways to find out the tables. Hence changing the names of the prefix is of no use. Moreover modifying the default prefix can cause several plugins to misbehave.
Furthermore, changing the database prefix midflight is difficult to implement and can cause your website to crash. This is because there are many changes that need to be made on every level. Any error in the process will prove to be catastrophic to your site.
3. Avoid Hiding Your Login Page
There is always someone trying to break into your site by cracking your password. During brute force attacks, hackers try to log into your website using a combination of popular usernames and passwords. So what if we hide the login page? That will kill two birds with one stone, right? Hacker wouldn’t be able to find the login page and the load on your server will be reduced.
WordPress has a default login page. URL to the page usually looks like this example.com/wp-login.php. One well-known way of saving your website from brute force attack is by hiding or changing the default login page to something else like example.com/mylogin.php. Although this sounds like a foolproof plan, let’s find out how effective the method is in keeping your WordPress site secure.
Server Load Reduction
After you hide or change the location of your login page, every time someone tries to open it, they’ll face a 404 error. However, login attempts are a heavy process. Whenever the 404 error page loads, it eats up a lot of your server resources. And ends up slowing down your website. Hence, the common belief that hiding your login page will reduce the load on the server is incorrect.
Alternative URL Not Hard to Guess
Part of WordPress’ success as a CMS is due to plugins that make modifications to a website easier. It’s not surprising that a popular way of hiding a login page of a site is by using a plugin. These plugins come with a set of default alternative login URL like xzy.com/wplogin.php, etc. We have been trained to just go with default settings. Once we install the plugin and change our URL, we don’t give much thought to it. But there are only so many URL a plugin can offer. It’s not too difficult to find out these preset login URL. Therefore, using alternative URL may be ineffective in most cases.
Usability Issues
The beauty of WordPress is that it’s easy to use. It’s a familiar platform. For a site with a multitude of users, changing or hiding the login page could pose certain issues. Several times we have come across posts on WordPress forums where users are locked out of a site because of a change in the login URL. In most case the changes were made using a plugin and the users were not made aware of the situation causing chaos.
4. Don’t Block IP Addresses Manually
If you have a security plugin installed on your site, you’ll be notified whenever someone tries to log into your website. You can easily get hold of the IP sending those malicious requests and block them using the .htaccess file. It’s a manually intensive work and not a very convenient practice.
Not User-Friendly
A non-technical person trying to modify the .htaccess files is a recipe for disaster. A content management system like WordPress has very strict formatting. Even using the most popular tools like FTP/SFTP are very risky. A minor error or an incorrect placement of command can cause the site to crash.
Too Many IPs to Block
To avoid getting blacklisted, hackers use IP addresses from around the globe. Previously, we discussed about manually blocking IP addresses who are constantly trying to break into your site. The work (as we’ve mentioned before) requires a lot of time and effort but isn’t exactly a very efficient use of time. But if you use any of top WordPress security plugins, for instance, Malcare, you can automate the blocking process. Such security plugins take care of all WP security loopholes.
5. Hiding WordPress
There is a general assumption that concealing your CMS makes it harder for people with vile intention to break into your site. What if we could hide the fact that your website is running on WordPress. That would protect your site from hackers wanting to exploit common vulnerabilities. An easy way of doing this is by (you guessed it) using a plugin. But the method fails when the hackers don’t care what platform your website is running on. Besides, there are a multitude of ways to find out if a site is running on WordPress.
Besides using a plugin, one can choose to do the work manually. But it’s a time-consuming process. A single WordPress update can undo all you work within a few seconds. Which means, you’d either have to repeat the process over and over again or shy away from WP updates. Skipping WordPress updates is like opening the front door for a hacker to walk right into your home.
6. Password Protecting wp-admin Does Not Work
The default WordPress login page (that looks like this – example.com/wp-admin) is a gateway to your site. A typical login page looks like the picture below.
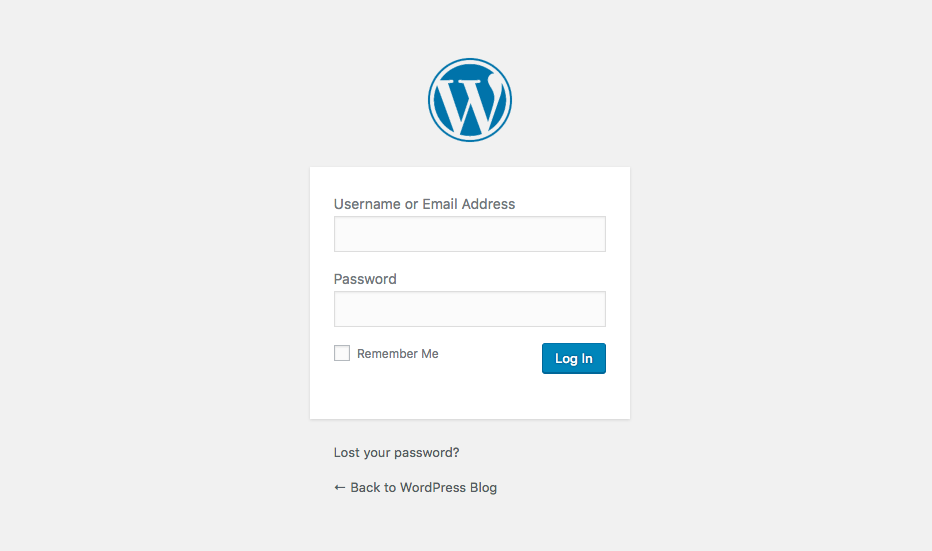
Here you’ll need to use your credentials to access the WordPress dashboard. Password protecting the login page helps hide or protect this gateway to the dashboard. It’s a good idea but not without its loopholes.
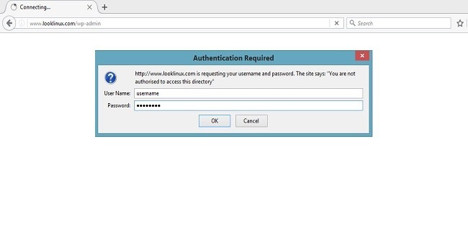
Picture courtesy: LookLinux
First off, it’s difficult to maintain or even change the password, if you happen to lose it. Besides being ineffective in providing additional security, such modifications to your site can prove to be very dangerous. For instance, when you password protect the admin page, request such as /wp-admin/admin-ajax.php cannot bypass the protection. There are plugins that could be dependent on the Ajax functionality of your site. And when they are not able to access this functionality, they start misbehaving. Hence, this can cause the website to break.
Over to You
If you have any questions or suggestions regarding what one needs to avoid to secure one’s WordPress site, let us know in the comments.




I often see the argument for changing the default WP login URL and how important it is for security. Yes, certain security plugins offer this capability but it is just as a gimmick to appease all the people asking for it. Don’t fall for the gimmick and think one security plugin is better than another because you can mask the WP login URL. Flawed thinking and it can be ruinous to WordPress.
You mention 3 good reasons why NOT to change the default admin URL but there is one more. It can break a lot of stuff. I have experienced more than my fair share of issues by changing the default login URL. I won’t name any names but one of the most popular security plugins that lets you change it also causes more issues than any other security plugin. If WordPress is no longer usable after installing a security plugin then it did a bit too good of a job. It keeps EVERYONE out 🙂
I have had many sites, a lot with a hide url; it does cut down a lot on the random lazy bot log in attempts. A good secure log in always helps anyway, but it does stop the chancer. I haven’t experienced any site being broken or areas not working due to this, nor has their been a user log in issue as they are always given a tiny url to log in that has the hidden post built in.