5 Default Security Threats in WordPress (Plus Fixes)

WordPress is a massively popular, completely open source piece of software. The great thing about that security-wise, is that there is a huge community that work with it, who are able to discover bugs as well as security risks quicker than one might with an in-house CMS solution. (It’s hard to find out about weaknesses when one way to find out is actually having the weakness exploited, and having a huge user base makes discovery a lot more likely.)
The downside is that hackers with bad intentions know exactly how your website is built. They already have the ‘blueprint’ to your site. And if there are any weaknesses in the core, themes or plugins that you use, that’s something they will be able to know without ever gaining access to the backend of your site.
So in this post, I’ll show you how to fix 5 security threats that are present in any completely default installation of WordPress. (If you’ve already taken some precautions, you might find that you’ve already fixed one or two, but it’s important to fix all five to minimize your risk of being hacked.)
Your Site Shows You’re Using WordPress, Plus The Version

The default version of WordPress will have lines of code that give away that your site is built using WordPress, even down to the version to people who know where to look. Depending on the theme, it might even be showed visually on every page of your website.
The reason this could be a security risk, is that people might target your site for no other reason than that it is built on WordPress. If someone finds a security weakness in the WordPress core, a theme or plugin, they might find their way to your site to exploit that. Whereas if you had successfully hidden that your site was built with WordPress, people who search for WordPress sites using bots or crawlers would be tricked into thinking that your site was not a viable target.
How to fix it:
To fix this, you can use the Hide My WP Plugin. With this helpful little plugin you can avoid unnecessary traffic on your server, and at the same time, remain safe from attacks that specifically target WordPress sites.
Everyone Knows Where Your Login Page/Admin Area Is Located
If you’re still showing that you use WordPress (aka, not actively hiding it by for example using a plugin like Hide My WP), people with bad intentions will already know where to attempt a brute-force attack on your site.
How to fix it:
To fix this threat, and drastically lower the chances of getting hacked, and to reduce server stress, we need to stop malicious people and bots from reaching our login page.
There are two main ways to do this. You can either change the physical location of your login page to something else by using a plugin (or a few lines of code), or you can limit the access to your login page and admin area by IP addresses. You can do this with a plugin dedicated to this particular thing, or with a security plugin like Sucuri, Wordfence, Solid Security Pro or All In One WP Security & Firewall.
WordPress Has A Default Table Prefix That Everybody Uses

A table prefix is what comes before names of tables in your database. Instead of users, with the standard WordPress prefix, it would be wp_users. If you use the default table prefix it makes it easier for people to gain access to your site by exploiting possible sql injection weaknesses. Because they know exactly where to inject info into your database to then gain access to your site.
I actually had one of my websites hacked because of sql injection, so this is a very real threat that you need to take countermeasures against.
How to fix it:
Thankfully it’s very easy to remove this threat. If you’ve already installed WordPress using the default wp_ prefix, you can easily change it using a plugin like Sucuri. First, you need to backup your database before you use that option as there is a minor chance of something going wrong. You can do this with the click of a button. Then you can choose a new prefix, or simply let Sucuri randomly generate the new prefix for you.
Note: If you’re just installing WordPress for the first time, you can change it in the installation interface.
WordPress Theme & Plugin Files Are Editable Via The Dashboard
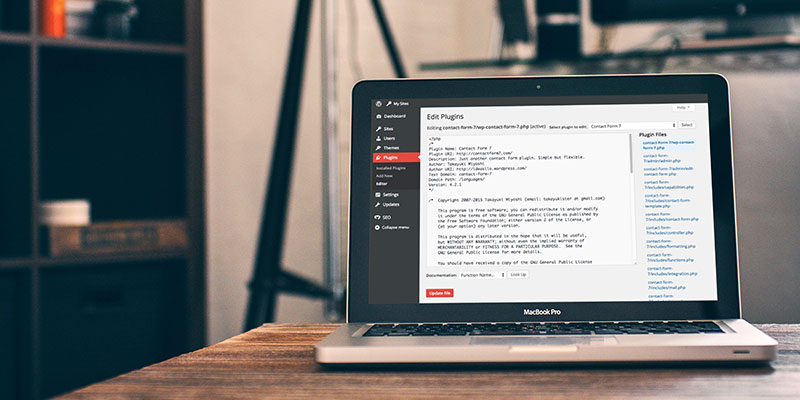
The problem with this, is that if a hacker gains access to your website, they can do a lot of damage. They can make your website infest other people with malware (which could end with your site getting put on Google’s blacklist and deindexed from search engines), deface your website, or easily open up backdoors.
How to fix it:
You can either add this line of code to your wp-config.php file:
define( 'DISALLOW_FILE_EDIT', true );Or use a security plugin to do it for you (that will basically only insert that line of code for you). The only problem is that there are plugins that allow people to turn this ability on and off, so a very dedicated hacker might be able to install a plugin, turn the plugin on, and then gain access to editing code without FTP access.
If you want to be extremely thorough and protect against this, you can disable all plugin and theme updates/installation by adding this line of code to wp-config.php:
define( 'DISALLOW_FILE_MODS', true );But obviously this would mean you would have to change it’s value to false every time you wanted to update or install a plugin or theme (we don’t really recommend this option, since keeping themes and plugins up to date is one of the best ways to ensure your site is less vulnerable).
WordPress Has Very Open Firewall Settings That Can Allow Even Known Malicious Bots To Attempt Attacks

The default firewall settings of WordPress are actually on the liberal side. This means that some untoward bots and other unwanted visitors get a green light.
How to fix it:
You can make this better by installing the basic 5G blacklist firewall rules, by either copying it manually into your .htaccess file, (you can find it here) or by installing this plugin, or use a security plugin to better optimize the rules in your .htaccess.
Unlimited WordPress Login Attempts
While the default setting is indeed unlimited login attempts, you may have chosen to limit login attempts when you installed WordPress on your site. If you did not, however, it’s an incredibly easy fix.
How to fix it:
Simply install the Limit Login Attempts plugin. Or, if you’re using WPEngine hosting this is a feature they’ve already built-in for you – no plugin required! If you already protect your login area by only allowing your own IP addresses to access the dasbhboard, you won’t need to do this. But if you just hid your login page’s address, it’s a nice double protection from potential brute-force attacks.
Conclusion
Cyber crime is rapidly growing and the internet is on it’s way becoming home to more criminals than ‘the real world.’ In some countries this has already happened. And while much of this is credit card and bank fraud, there is a growing number of hackers out there, and as website owners we have to protect ourselves and our sites as best we can.
While a default installation of WordPress has some weaknesses, the beauty of WordPress is really in the ease of which you can solve pretty much any of your problems with your site, including the security threats mentioned in this post. Beyond having a unique username and a strong password, by installing a security plugin, editing some settings and maybe inserting a line of code or two, you can already significantly reduce the risk of your site getting hacked or infested with malware.
Have you taken any measures to improve the security of your WordPress site? What kind? We’d love to hear some of your tips & tricks! Please let us know in the comments.