Common WordPress Attacks and How to Stop Them

WordPress has been one of the leading content management systems (CMS) for more than a decade. Many of the internet’s largest blogs, as well as plenty of small, individual sites, run on the WordPress framework for publishing text, image, and video content to the world wide web.
A WordPress website has both a front-end and back-end interface. The front-end provides the view that outside visitors will see when they load the webpage. The back-end can be accessed by site administrators and contributors who are responsible for drafting, designing, and publishing content.
Like every other internet-based system, WordPress is a target of hacking attempts and other forms of cybercrime. Which makes sense considering now more than 32% of the internet runs on WordPress. In this article, we’ll run through some of the most common WordPress attacks on the software and then offer suggestions for how to defend against them and keep your website secure.
Methods of Common WordPress Attacks
First let’s look at the common attack WordPress site owners might run into.
1. SQL Injection
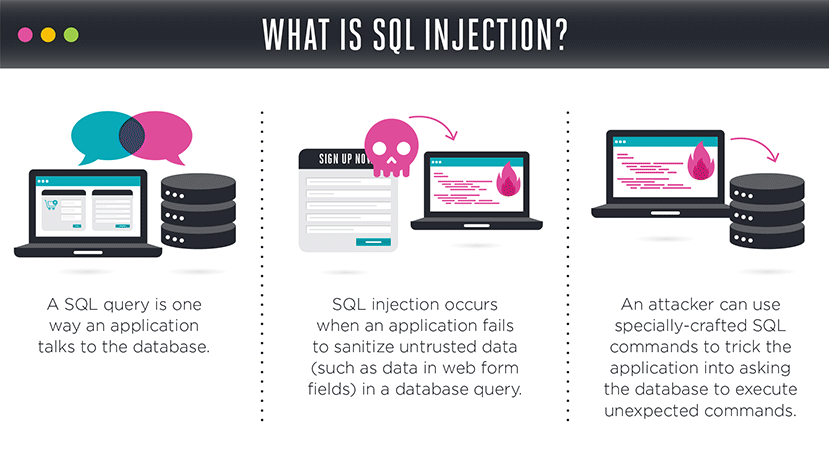
The WordPress CMS platform relies on a database layer that stores metadata information as well as other administrative information. For example, a typical SQL-based WordPress database will contain user information, content information, and site configuration data.
When a hacker carries out a SQL injection attack, they use a request parameter, either through an input field or a URL, to run a customized database command. A “SELECT” query will allow the hacker to view extra information from the database, while an “UPDATE” query will allow them to actually change data.
In 2011, a network security company called Barracuda Networks fell victim to a SQL injection attack. The hackers ran a series of commands across the entire Barracuda website and eventually found a vulnerable page which could be used as a portal to the company’s primary database.
2. Cross-site Scripting
A cross-site scripting attack, also known as XSS, is similar to SQL injection accept it targets the JavaScript elements on a webpage instead of the database behind the application. A successful attack can result in an outside visitor’s private information being compromised.
With an XSS attack, the hacker adds JavaScript code to a website through a comment field or other text input, and then that malicious script is run when other users visit the page. The rogue JavaScript will typically redirect users to a fraudulent website that will attempt to steal their password or other identifying data.
Even popular websites like eBay can be targets of XSS attacks. In the past, hackers have successfully added malicious code to product pages and convinced customers to log in to a spoofed webpage.
3. Command Injection
Platforms like WordPress operate on three primary layers: the web server, the application server, and the database server. But each of these servers is running on hardware with a specific operating system, such as Microsoft Windows or open-source Linux, and that represents a separate potential area of vulnerability.
With a command injection attack, a hacker will enter malicious information in a text field or URL, similar to a SQL injection. The difference is that the code will contain a command that only operating systems will recognize, such as the “ls” command. If executed, this will display a list of all files and directories on the host server.
Certain internet-connected cameras have found to be especially vulnerable to command injection attacks. Their firmware can improperly expose system configuration to outside users when a rogue command is issued.
4. File Inclusion
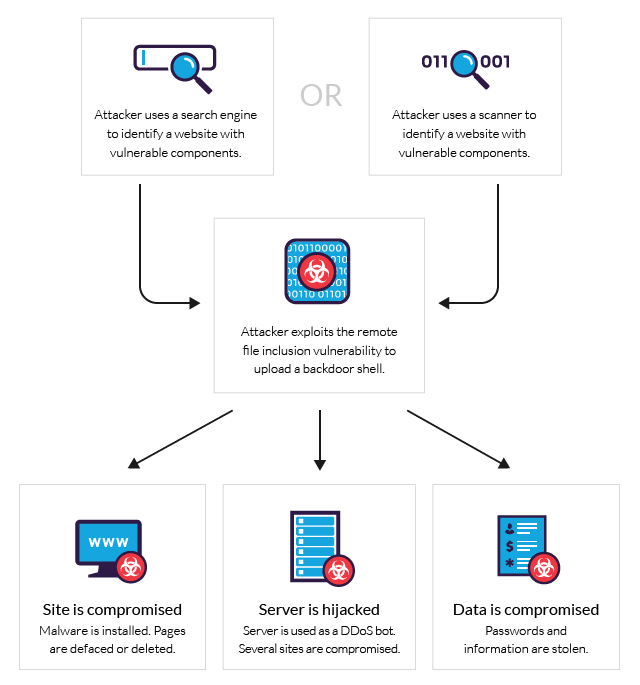
Common web coding languages like PHP and Java allow programmers to refer to external files and scripts from within their code. The “include” command is the generic name for this type of activity.
In certain situations, a hacker can manipulate a website’s URL to compromise the “include” section of the code and gain access to other parts of the application server. Certain plug-ins for the WordPress platform have been found to be vulnerable against file inclusion attacks. When such hacks occur, the infiltrator can gain access to all data on the primary application server.
Tips for Protection
Now that you know what to be on the lookout for, here are a few easy ways to harden your WordPress security. Obviously, there are many more ways to secure your site than are mentioned below, but these are relatively simple methods to start with that can yield impressive returns in hackers thwarted.
1. Use a Secure Host and Firewall
The WordPress platform can either be run from a local server or managed through a cloud hosting environment. For the purpose of maintaining a secure system, the hosted option is preferred. The top WordPress hosts on the market will offer SSL encryption and other forms of security protection.
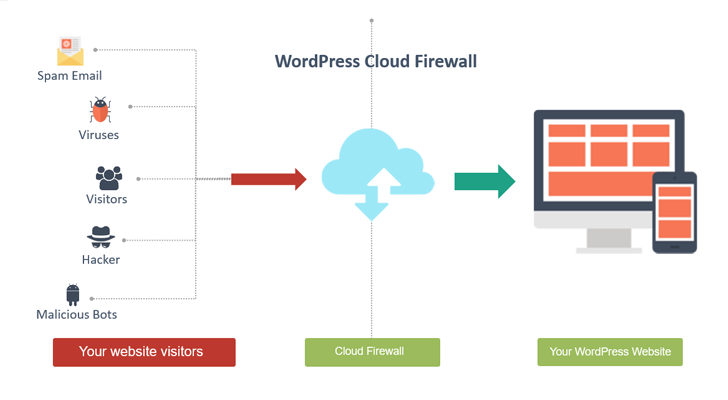
When configuring a hosted WordPress environment, it’s critical to enable an internal firewall that will protect connections between your application server and other network layers. A firewall will check the validity of all requests between layers to ensure that only legitimate requests are allowed to be processed.
2. Keep Themes and Plugins Updated
The WordPress community is filled with third-party developers who are constantly working on new themes and plugins to leverage the power of the CMS platform. These add-ons can either be free or paid. Plugins and themes should always be downloaded directly from the WordPress.org website.
External plug-ins and themes can be risky, as they include code that will be run on your application server. Only trust add-ons that come from a reputable source and developer. In addition, you should update plugins and themes on a regular basis, as developers will release security improvements.
Within the WordPress admin console, the “Updates” tab can be found at the very top of the “Dashboard” menu list.
3. Install a Virus Scanner and VPN
If you are running WordPress in a local environment or have full server access through your hosting provider, then you need to be sure to have a robust virus-scanner running on your operating system. Free tools to scan your WordPress site like Virus Total will check all resources to look for vulnerabilities.
When connecting to your WordPress environment from a remote location, you should always use a virtual private network (VPN) client, which will ensure that all data communications between your local computer and the server are fully encrypted.
4. Lockdown Against Brute Force Attacks
One of the most popular and common WordPress attacks takes the form of so-called brute force attacks. This is nothing more than an automated program a hacker turns loose at the “front door.” It sits there and tried thousands of different password combinations and stumbles across the right one often enough to make it worthwhile.
The good news is that there is an easy way to foil brute force. The bad news is that too many site owners don’t apply the fix. Check out the All in One WP Security and Firewall. It’s free and allows you to set a hard limit on login attempts. For example, after three attempts the plugin locks the site down against further logins by that IP address for a preset length of time. You’ll also receive an email notification that the lockdown feature has been triggered.
5. Two-Factor Authentication
This nifty method of securing your site relies on the fact that hacker likely won’t be able to assume control of two of your devices simultaneously. For example, a computer AND cell phone. Two-Factor Authentication (2FA) turns logging into your Website website into a two-step process. As usual, you log in the regular way but then will find yourself prompted to enter an additional code sent to your phone.
Clever, huh? This one extra step increases the security of your site exponentially by separating the login into different steps. Check this list of free plugins that will help you set up 2FA. Those hackers that were thinking of trying to mess with your site are probably already changing their minds.
Conclusion
While there is no such thing as a 100% secure website, there are plenty of steps you can take to protect your website. Using a good firewall, keeping your themes and plugins up to date and periodically running a virus scan can make a huge difference.
It might help to think of website security as an eternal iterative process. There should never come a point when you step back and think it is “complete” because the game between hackers and website defenders will never stop, with even officially-sanctioned online players getting into the online surveillance business . Only by keeping yourself knowledgeable about the latest threats and how to repel them will you be able to maintain cybersecurity and online privacy.
It’s too bad the world has to be this way but accept it and move on. If you’ve never done it before, now would be a good time to locate a few respected cybersecurity news sites. Either subscribe to their newsletter or at least pay regular visits. Get started by running a Google (or the search engine of your choice) search for “cybersecurity news.”
Have a question, or more tips to add? Leave a comment and let us know.



Good information! Thanks for the information. I had been following some of tips but not all. I have PureVPN installed on my system, especially when I’m on Public WiFi, and I do use VirusTotal but that’s just user end. Is Sucuri a good choice to protect my website? Or these tips would do?
A VPN is great to be sure you’re using a private/secure connection when logging into your website, and VirusTotal is an antivirus you can use to manually scan files (or at least that’s my understanding of it – I haven’t used it myself). VaultPress is an automated and secure plugin to scan (and repair) files as well as take full backups of your website. So on the off chance something bad does happen, you have complete database backups that you can restore with just a click (plus VaultPress memberships also include Akismet to protect your site from copious amount of spam). I would definitely recommend using VaultPress or taking your own manual backups as an added layer of site security (here’s a helpful guide on how to backup WordPress).
Try using the Booster plugin, it can help you instantly by Rate Limit and reject links Technology.
Thanks for sharing – this looks like a great option to monitor and block bots.
As secure as WordPress can be, when updated on a regular basis, its security isn’t always foolproof. Thus, it’s good to see tips like these offered so that website owners, businesses, and the like will be able to protect their digital assets.